At a Glance
2025–2026 policy shifts made many crypto activities broadly permissible for banks, shifting executive focus from approval hurdles to disciplined operational execution, third-party control, and resilience.
What changed in 2025
Across 2025, supervisory posture shifted in a way executives should interpret as a higher operational bar rather than a lighter regulatory burden. The practical threshold for basic permissibility moved downward, but the expectation for demonstrable safety and soundness moved closer to the front of the exam cycle. For banks, that translates into faster paths from concept to activity, paired with less tolerance for weak control evidence, unclear accountability, or immature third-party oversight.
The OCC’s direction is broadly consistent with a move away from bespoke prior approval mechanics and toward routine supervision and enforcement levers. That framing matters because it changes how digital asset activity will be judged: not as a one-time permissioning event, but as an enduring line of business that must fit within existing risk taxonomy, control testing, and operational resilience programs.
OCC permissibility becomes table stakes
The rescission of Interpretive Letter 1179 removed the prior supervisory non-objection construct that had functionally extended decision timelines and raised governance friction. Subsequent interpretive letters in 2025 reinforced that a range of crypto-related activities can be treated as incidental to banking when conducted within the bank’s established risk management framework, including holding certain crypto assets to pay network fees, conducting testing in controlled environments, and facilitating certain riskless principal transactions.
Executives should treat this as a reclassification of the debate. The central question is no longer whether an activity is theoretically permissible, but whether the bank can operate it with a control posture that will withstand routine supervisory scrutiny across operational risk, liquidity and funding risk, financial crime compliance, model and technology risk, and third-party risk management.
Expanded perimeter and operational focus
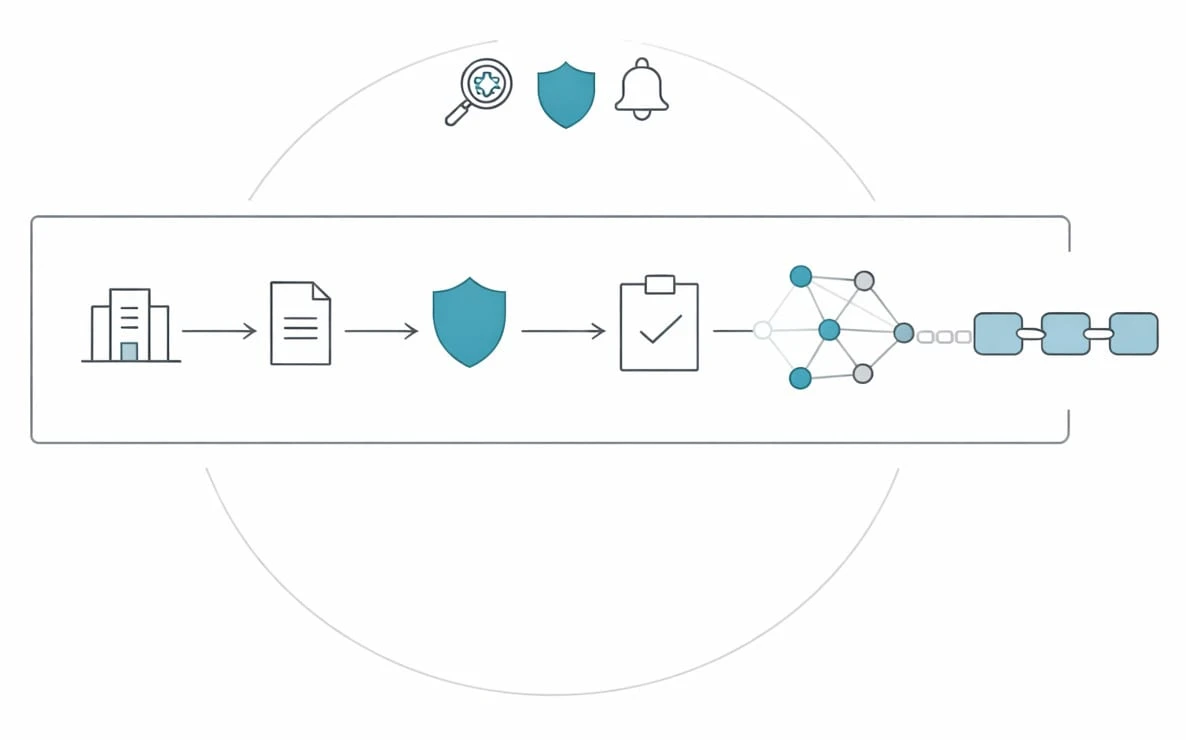
As permissibility clarifies, the regulatory perimeter expands in a different way: more activities fall inside the bank’s operating model, and therefore inside its control perimeter, audit scope, and resilience obligations. This is where digital asset initiatives often encounter their true constraints, including the need to prove end-to-end control effectiveness across novel transaction flows, new operational dependencies, and less familiar failure modes.
Operational risk shifts from an abstract concept to an exam artifact
Blockchain architectures introduce distinct operational risks that traditional control libraries do not always capture cleanly. Key management, transaction finality, smart contract dependencies, network congestion and fee volatility, and continuous processing windows can create operational exposures that look more like high-availability payments and market infrastructure than like classic custody or balance sheet products.
To meet supervisory expectations, banks need traceable control evidence for core operational disciplines: clear lines of accountability, rigorous change management, incident and problem management tied to business impact tolerances, and recovery capabilities that assume degraded third parties and stressed market conditions. Where activities are “always on,” resilience engineering becomes a business requirement, not simply a technology design preference.
Third-party governance becomes the fulcrum
Even when core capabilities are built in-house, most operating models rely on third parties for custody technology, blockchain analytics, market connectivity, and specialized operational services. Supervisory attention therefore concentrates on whether the bank can govern outsourced components with the same rigor applied to internally managed services, including contract and SLA discipline, access and key control, ongoing performance monitoring, concentration risk management, and exit feasibility.
For executive committees, the practical trade-off is speed versus controllability. Outsourcing can accelerate launch timelines, but it can also concentrate operational and compliance dependencies in a few counterparties, creating correlated failure risk and limiting the bank’s ability to evidence control effectiveness during exams.
Financial crime and liquidity controls stay non-negotiable
Clarity on permissibility does not relax expectations around BSA and AML compliance, sanctions controls, or fraud risk management. Digital asset flows can increase monitoring complexity, especially where on-chain activity, off-chain customer behavior, and third-party service operations must be joined into a single investigative narrative.
Liquidity and funding governance also deserve explicit board attention. Network fee dynamics, settlement timing differences, intraday liquidity impacts, and the operational ability to halt or reroute activity under stress can all become binding constraints, particularly when products or pilots scale beyond an initial client cohort.
Market adoption accelerators and new supervisory questions
The GENIUS Act established a more formal federal framework for bank-issued payment stablecoins, moving stablecoin activity closer to mainstream payment and deposit-adjacent governance expectations. As market infrastructure tests emerge, including tokenization pilots that emphasize “always-on” settlement concepts, banks face a new class of supervisory questions that look familiar in principle but demanding in execution.
Stablecoins move from policy debate to operating model design
For banks evaluating stablecoin issuance or participation, the policy environment reduces ambiguity while increasing the requirement for a disciplined product operating model. Governance must define what the stablecoin represents economically, how reserves are managed and evidenced, how redemption mechanics perform under stress, and how customer and market conduct risks are addressed. These questions are best treated as extensions of payments and liquidity governance, with additional technology, cyber, and third-party dimensions.
Tokenized settlement forces decisions on continuous controls
Tokenized settlement initiatives introduce the prospect of shorter settlement cycles and new asset servicing mechanics, but they also force control redesign. Continuous processing windows require continuous controls: monitoring, limits, reconciliation, exception handling, and incident response must work outside standard business hours. That can pressure staffing models, oversight rhythms, and the ability of second line functions to remain effective in near real time.
Chartering and supervisory perimeter signals matter
Developments such as conditional national trust charters and supervised pilots can enable new participation models. For bank executives, the key governance implication is boundary management: deciding which activities reside in the bank, which sit in affiliates, and how shared services, data, and controls will be governed to avoid creating gaps that supervisors will interpret as unmanaged risk.
De-risking execution decisions with a digital maturity lens
As permissibility becomes less of a gating item, leadership teams need a repeatable way to test whether capabilities are truly ready for supervisory scrutiny at scale. A maturity assessment provides that discipline by mapping strategy and product intent to the bank’s actual ability to operate safely across governance, risk ownership, control design, resilience, data, and third-party oversight. Used well, it reduces the chance that a permissible activity becomes an operational incident, a compliance breakdown, or a remediation program.
In practice, DUNNIXER can be used as a structured benchmark for this readiness through the DUNNIXER Digital Maturity Assessment, helping executives evaluate sequencing and decision confidence against the same constraints raised by OCC supervision and the GENIUS Act framework. The most useful output is not a score, but a clear view of where the operating model will fail under stress, which control proofs are missing for exam readiness, and which third-party dependencies create concentrated operational risk.
Reviewed by

The Founder & CEO of DUNNIXER and a former IBM Executive Architect with 26+ years in IT strategy and solution architecture. He has led architecture teams across the Middle East & Africa and globally, and also served as a Strategy Director (contract) at EY-Parthenon. Ahmed is an inventor with multiple US patents and an IBM-published author, and he works with CIOs, CDOs, CTOs, and Heads of Digital to replace conflicting transformation narratives with an evidence-based digital maturity baseline, peer benchmark, and prioritized 12–18 month roadmap—delivered consulting-led and platform-powered for repeatability and speed to decision, including an executive/board-ready readout. He writes about digital maturity, benchmarking, application portfolio rationalization, and how leaders prioritize digital and AI investments.
References
- https://www.sidley.com/en/insights/newsupdates/2026/01/the-state-of-play-in-banking-and-digital-assets-welcome-developments-from-the-banking-agencies
- https://alessa.com/blog/the-2025-aml-crackdown/
- https://www.dailyjournal.com/mcle/1720-stablecoins-gain-clarity-under-genius-act-as-legal-questions-linger-for-banks-and-fintechs
- https://financialcolumnist.com/?view=article&id=32:from-permission-to-preparedness-u-s-regulators-shift-on-crypto&catid=36#:~:text=The%20impact%20is%20sweeping:%20OCC%20(%20the,a%20safeguard%20and%20more%20as%20a%20deterrent.
- https://acceleronbank.com/articles/articles/stablecoins-genius-act-community-banks#:~:text=That%20changed%20in%202025.%20Early%20in%20the,long%2Dawaited%20federal%20framework%20for%20issuing%20payment%20stablecoins.
- https://business.cch.com/BFLD/VB_GENIUS-Act_08-27-2025_final.pdf#:~:text=In%20early%202025%2C%20the%20OCC%20issued%20Interpretive,while%20dropping%20an%20earlier%20supervisory%20non%2Dobjection%20requirement.
- https://orx.org/blog/managing-the-shifting-regulatory-landscape#:~:text=The%20regulatory%20landscape%20is%20about%20to%20see,regulation%20in%20the%20US%20and%20other%20regions.
- https://www.clearstream.com/resource/blob/2620054/7d4925e094df7fa997ea845edf423104/product-info-fx-services-data.pdf#:~:text=Successive%20waves%20of%20regulatory%20change%20have%20made,exposure%20is%20crucial%20in%20today's%20business%20environment.
- https://kpmg.com/xx/en/our-insights/risk-and-regulation/the-2026-kpmg-global-third-party-risk-management-survey.html#:~:text=Third%2Dparty%20risk%20management:%20Navigating%20complexity%20in%20a,drivers%20shaping%20TPRM%20strategies%20across%20the%20globe.
- https://www.grantthornton.in/globalassets/1.-member-firms/india/assets/pdfs/operational_risk_management_and_operational_resilience.pdf#:~:text=The%20regulator%20widely%20recognises%20the%20need%20for,managing%20operational%20risk%20remains%20a%20significant%20challenge.
- https://www.debevoise.com/insights/publications/2025/03/occ-takes-initial-steps-to-liberalize-approach-to#:~:text=Overview,safe%20and%20sound%20banking%20practices.%E2%80%9D
- https://www.mondaq.com/unitedstates/fin-tech/1711200/occ-confirms-banks-permitted-to-pay-gas-fees#:~:text=On%20November%2018%2C%202025%2C%20the%20Office%20of,network%20fees%20on%20blockchain%20networks%20(%22gas%20fees%22)
- https://www.dwt.com/blogs/financial-services-law-advisor/2025/11/occ-crypto-assets-for-network-gas-fees#:~:text=Gas%20Included:%20OCC%20Clarifies%20That%20Banks%20May,%22gas%20fees%22%20and%20to%20test%20crypto%20platforms.
- https://www.jdsupra.com/legalnews/occ-confirms-riskless-principal-6523616/#:~:text=On%20December%209%2C%202025%2C%20the%20OCC%20issued,transactions%20in%20assets%20that%20are%20not%20securities.
- https://www.sidley.com/en/insights/newsupdates/2026/01/the-state-of-play-in-banking-and-digital-assets-welcome-developments-from-the-banking-agencies#:~:text=The%20OCC%20further%20confirmed%20that%20national%20banks,third%2Dparty%20risk%20management%20practices%20are%20in%20place.